Consolidating the visibility across the entire OT environment, iSID bolsters security posture and compliance with emerging cyber regulations and directives
AUTO-LEARNING
Automatic generation of baseline topology and behavior model including all devices, ports, and connections
NON-INTRUSIVE ANALYSIS
DPI protocol-based analysis of mirrored network traffic stream with no disruption of operations
CENTRALIZED OR LOCAL DEPLOYMENT
Centralized deployment using iSAP Smart Collectors or local deployment at remote sites
PLC MONITORING
Continuous supervision of configuration changes in PLCs and other network devices
ATTACK VECTOR ANALYSIS
Detection of down-vector vulnerabilities caused by networked device interoperability
MSSP-READY
Central management of multiple iSID instances at MSSP SOC
iSID provides security personnel with visibility of devices, protocols, and sessions, detection of threats and attacks, policy monitoring and validation of operational parameters, and networked device management. Upon initial deployment, iSID monitors the network, devices, and communications, and establishes a baseline of normal behavior. Passively monitoring network traffic, it determines deviations from proper behavior, detecting anomalies which may be indicators of compromise.
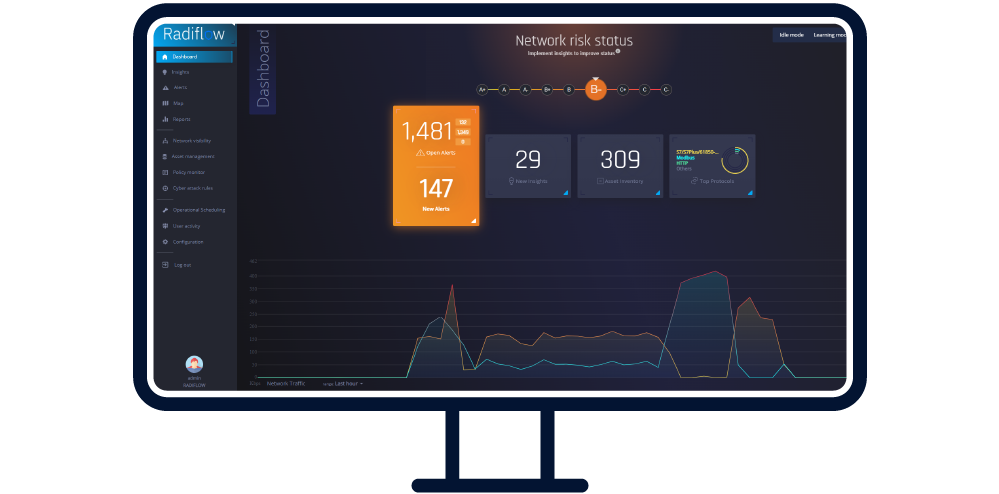
Network Visibility: Via passive scanning of all OT network traffic, iSID creates a visual network model for all devices, protocols, and links. Map View displays graphical representations of all network devices in multiple, helpful display modes like Purdue, Flow, Analyst, and Custom. Maps are zoomable and elements can be dragged to any location on the screen.
Asset Inventory Management: iSID automatically discovers assets and builds an accurate asset inventory that includes roles and their impact on the OT environment. It monitors generations of legacy and modern asset types as well as their communication protocols. For convenient management, it separates out illegitimate assets and reduces alerts on them. In mixed IT/OT environments, iSID automatically groups internet-facing assets and manages them separately. It presents all system assets, categorized and filterable by type (PLC, Server, HMI, Engineering Station, Broadcast, etc.) or by any asset characteristic. Asset types are automatically detected by iSID; the user can change each asset’s designation or add custom asset types.
Policy Monitoring: Based on its automatic learning, iSID creates relevant policy suggestions that can be adjusted and approved for precise implementation. Users may define and modify policies for validating specific commands (“write to controller”) and operational ranges (“do not set turbine above 800 rpm”). Internet-facing assets are highlighted. Continuous supervision of configuration changes in PLCs and other network devices prevents unauthorized and inadvertent disturbances to smooth operation.
Vulnerability Management: iSID keeps up with the latest threat intelligence as well as SNORT-based signatures, common attack signatures, and vulnerabilities, enabling it to quickly detect anomalies before they can cause damage. Accurate identification and mapping of publicly known vulnerabilities (CVEs) keep industrial sites free of cyber threats. Asset Patch Management helps security personnel keep up with necessary and important updates.
Anomaly Detection: iSID automatically creates a behavioral network model using multiple parameters, including device sequence sampling time, frequency of operational values and more, enabling it to quickly detect behavioral anomalies.
Operational Behavior: iSID monitors and audits the management of devices (PLC, RTU, IED) at remote sites, furnishing alerts for firmware changes or configuration modifications such as software updates or turning edge devices on or off. It also logs activity.
Cyber Attack: iSID handles known threats to the network, including PLCs, RTUs, and industrial protocols, based on data gathered from across the cybersecurity research community.
Alert Management: iSID classifies assets in the operational environment, eliminating alert noise. It helps security practitioners respond effectively by displaying alerts by type and severity class for identification and efficient handling of the most important alerts.