THE STORY:
A notorious Iranian hacker group, “APT33”, has been observed shifting its targets from IT networks toward critical industrial (OT) infrastructures such as power generation, manufacturing and oil refineries. It is unclear at this time whether APT33 is a nation-state actor funded or run by the Iranian government, as claimed by some sources.
Considering APT33’s track record in wreaking havoc in IT networks (notably, using the Shamoon data-wiping malware), it’s clear that this shift from IT to OT poses a great threat of disruption of national critical services.
Interestingly enough, a few days after the ABT33 story was published, news broke that IBM X-Force detected a new destructive wiper called ZeroCleare, which bears similarity to the Shamoon malware, and is suspected to have been used by another Iran-based group to target national energy and industrial Middle East.
[inject id=’code-47fd23f73a9caecab1e206306adae7f9′]
ANALYSIS:
- It is not yet clear why APT33 (and perhaps other groups) have chosen to shift their focus from IT to OT. If indeed the Iranian government is behind the group, it could mean that the ultimate goal is espionage or destruction of national assets, as opposed to merely collecting ransom or pursuing financial gains.
- Either way, one thing is clear: OT (ICS/SCADA/IIoT) networks are by and large much less protected and much more exposed to attacks than IT networks, especially networks with devices that hadn’t been designed with security in mind. Left inadequately protected, OT networks are no match for a new class of sophisticated, destructive malware such as Shamoon or ZeroCleare.
- At present, the types of attacks we expect to see at first from IT-hacker groups will focus on the server level (L2) rather than higher operational levels, that is more easily accessible through the IT-OT interface. That said, as hackers become more proficient we will surely see a progression toward higher network levels.
WHAT THIS MEANS TO YOU:
If you’re an ICS/SCADA operator, the time to take action and protect your network is now.
- At minimum, you should perform a network security assessment to map your assets and their vulnerabilities, and prioritize critical risk mitigation measures by business impact.
- Preferably you should also use a dedicated OT Intrusion Detection system for continuous monitoring of all network traffic for malicious activity and abnormalities.
- In the case of hybrid IT-OT networks, system operators need to focus their efforts on hardening the IT-OT interface to prevent bi-directional data transfer that may contaminate the OT domain (or, at minimum, allow only authorized and sanitized network traffic, essential to business activities, to pass through to the OT network).
- OT-specialized Managed Security Services Providers (MSSPs) have established themselves as a viable alternative to in-house security departments, saving both the cost and more importantly the OT-security expertise that is extremely hard to come by. MSSPs can offer a more holistic security and network management solution, including threat intelligence, periodic risk assessment, device obsolescence management, etc.
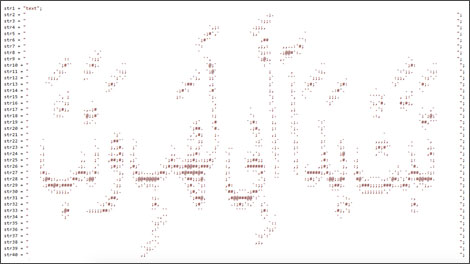
ASCII art found in the Shamoon v.3 toolkit depicting inflammatory Arabic text (Source: McAfee)


